IT Risk Management in Transition: From Reactive Security to Digital Sovereignty
IT infrastructure risks can no longer be viewed primarily as technical concerns. Cloud services, mobile work environments, and growing regulatory requirements mean that technical
vulnerabilities can quickly have business-critical impacts. As a result, IT risk management is becoming a strategic management responsibility with
board-level visibility.
IT risk management affects organizational stability, security, and long-term resilience. Organizations that address risks only after something goes wrong lose valuable time or, in the worst
case, control of their IT environment. Modern IT risk management begins much earlier, enabling organizations to proactively manage risks rather than merely react to
incidents.
IT Risk Management at a Glance
- Why a structured approach to IT risks determines an organization’s ability to act
- How a modern IT risk management process is designed
- The role of IT security risk management in achieving digital sovereignty
- Why prioritization matters more than maximum protection
- Why risk management in IT projects is critical to long-term success
Why a Reactive Approach to IT Risks Is No Longer Sufficient
For many years, IT risk management followed a simple principle: fix the security incident, stabilize systems, and move on. In today’s complex IT landscapes, this approach
is increasingly ineffective. Risks emerge simultaneously, are tightly interconnected across technical and organizational domains, and often affect business operations faster than
traditional processes can respond.
At the same time, regulatory and compliance pressures continue to intensify. Frameworks and regulations such as NIS2 and DORA require transparency,
traceability, and well-documented decision-making. Without a structured IT risk management process, organizations lack this foundation and, with it, the ability to actively
control risks rather than merely respond to them.
Transparency and Control as the Foundation of Digital Sovereignty
Digital sovereignty means being able to decide which risks are acceptable and which are not. This requires a clear overview of systems, dependencies, and security controls,
as well as transparent criteria for risk-based decisions.
A well-designed IT security risk management approach provides exactly this clarity. It combines technical visibility with organizational governance, ensuring that security
does not become a barrier to innovation. The result is a balanced approach between protection and agility — a key prerequisite for sustainable digital transformation and true digital
sovereignty.
Best Practices Guide: Strengthening Digital Sovereignty Systematically
This Best Practices Guide explains how organizations can holistically build digital sovereignty, spanning governance and security to a structured approach to IT risk
management. It provides practical recommendations to enhance transparency, control, and informed decision-making.
Download the Best Practices Guide now
What Defines Modern IT Risk Management Today?
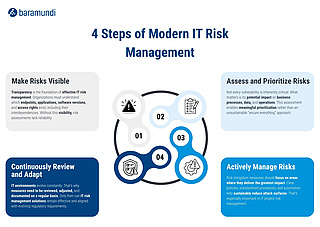
Contemporary IT risk management does not rely on rigid rulebooks. Instead, it follows a continuous, transparent process with four recurring steps:
1. Make Risks Visible
Transparency is the foundation of effective IT risk management. Organizations must understand which endpoints, applications, software versions, and access rights exist, including their
interdependencies. Without this visibility, risk assessments lack reliability.
2. Assess and Prioritize Risks
Not every vulnerability is inherently critical. What matters is its potential impact on business processes, data, and operations. This assessment enables meaningful prioritization rather
than an unsustainable “secure everything” approach and lays the groundwork for effective IT risk management tools and solutions.
3. Actively Manage Risks
Risk mitigation measures should focus on areas where they deliver the greatest impact. Clear policies, standardized procedures, and automation help sustainably reduce attack surfaces.
That’s especially important in IT project risk management, where early decisions determine whether risks are accepted, mitigated, or avoided.
4. Continuously Review and Adapt
Just as IT environments evolve constantly, security controls and risk mitigation measures must be reviewed and adjusted regularly. Only then can IT risk management solutions remain
effective, auditable, and aligned with evolving regulatory requirements.
IT Risk Management Extends Beyond the IT Department
The more deeply IT is embedded in business processes, the clearer it becomes that risks are not purely technical. Decisions on priorities, budgets, and new technologies directly shape an
organization’s risk profile.
This is especially evident in IT projects, where early risk assessment and clearly defined responsibilities are essential. When business units, IT teams, and leadership collaborate,
IT risk management becomes a unifying discipline rather than an isolated compliance requirement.
Conclusion: IT Risk Management Creates Security and Strategic Flexibility
IT risk management is neither an end in itself nor merely a compliance exercise. When implemented effectively, it provides clarity in complex IT environments, strengthens an organization’s digital sovereignty, and creates the strategic flexibility to innovate with confidence.