Vulnerability Management: Finding Security Gaps Before Attackers Do
New digital entry points are discovered every day. A missing patch here, a misconfiguration there—and suddenly a minor IT weakness turns into a serious security risk. Vulnerability
management ensures this doesn’t happen. It helps organizations identify vulnerabilities early, assess their real risk, and remediate them effectively—before attackers can exploit
them.
Why does this matter so much? According to the latest situation reports, more than 100 new vulnerabilities are disclosed every single day. Organizations that don’t manage
them systematically are effectively playing cyber roulette.
Vulnerability Management at a Glance
- Vulnerability management is a continuous process for identifying and remediating IT security weaknesses
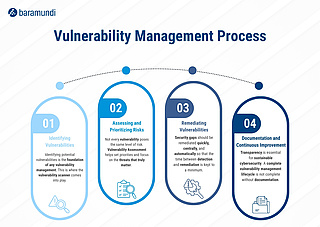
- A structured vulnerability management process includes detection, assessment, remediation, and documentation
- Vulnerability management tools and scanners enable automated vulnerability scanning
- The vulnerability management lifecycle integrates patch management, reporting, and compliance
What Is Vulnerability Management?
Vulnerability management — also known as vulnerability management in cyber security — is a continuous process used to identify, evaluate, prioritize, and remediate security
weaknesses in IT environments. Its primary goal is to minimize the attack surface and reduce risk before vulnerabilities can be actively exploited.
Unlike one-time security assessments, vulnerability management is not a project with a defined end date. It is an ongoing discipline that evolves alongside new threats,
technologies, and business requirements. Modern vulnerability management tools automate large parts of this process, ensuring that
vulnerabilities are not only detected but also tracked and resolved in a transparent, auditable manner.
What Are IT Vulnerabilities?
Vulnerabilities are weaknesses in hardware, software, or system configurations that allow attackers to gain unauthorized access to systems, networks, or sensitive data. They often result
from programming errors, outdated software, or improper configurations—but sometimes also from insecure design decisions.
Common types of vulnerabilities include:
- Known vulnerabilities are often particularly relevant because exploits and attack methods become available quickly. However, whether they are truly critical depends on the context — factors such as exposure, exploitability, asset value, and existing countermeasures all play a role
- Zero-day vulnerabilities are security flaws for which no patch is yet available or that are not yet sufficiently known to the vendor or operator to enable remediation
- Misconfigurations, such as open ports, default credentials, or overly permissive access rights
- Design and logic flaws that may have been deliberately accepted during the architectural design of applications
The number of vulnerabilities continues to grow steadily—especially in areas such as IoT, OT environments, and custom-developed software.
Whitepaper: Detect, prioritize, and remediate vulnerabilities—automated and structured.
Our whitepaper explains how modern vulnerability management works, the role of automation, and how organizations can close security gaps faster and more reliably.
Download the whitepaper now
The Vulnerability Management Process: How It Works
The vulnerability management process follows a clear, cyclical structure. Think of it as a recurring health check for your IT infrastructure.
1. Identifying Vulnerabilities
The foundation of any vulnerability management program is the identification of potential weaknesses. This step relies heavily on vulnerability management tools and scanners:
- Analysis of systems, ports, services, and software versions
- Correlation with known vulnerabilities (CVE databases)
- Inclusion of both IT and OT environments
Result: an initial overview of potential security gaps.
2. Assessing and Prioritizing Risks (Vulnerability Assessment)
Not every vulnerability poses the same level of risk. During the vulnerability assessment phase, findings are evaluated based on:
- CVSS score
- Exploitability
- Criticality of the affected asset
- Context (for example, internet-facing vs. internal systems)
Risk-based approaches help reduce false positives and focus remediation efforts on the vulnerabilities that truly matter.
3. Remediating Vulnerabilities
Security gaps should be addressed based on priority and risk. In practice, this includes:
- Patch management and Third Party Patching working hand in hand to deploy updates efficiently
- Configuration changes
- Compensating controls such as network segmentation
The key is balancing risk reduction against operational effort and business impact.
4. Documentation and Continuous Improvement
Transparency is essential for sustainable cybersecurity. A mature vulnerability management lifecycle always includes thorough documentation:
- Dashboards and reports
- Evidence for audits and compliance requirements
- Historical data to improve future remediation strategies
With each cycle, vulnerability management becomes more effective and more efficient.
How Does a Vulnerability Scanner Work?
A vulnerability scanner is a core component of modern vulnerability management tools. It automatically
scans IT environments for known vulnerabilities by analyzing open ports, running services, software versions, and configurations, and comparing them against up-to-date vulnerability
databases.
Based on this analysis, the scanner evaluates potential risk and provides actionable remediation guidance — such as patch recommendations or configuration changes. Integrated into the
vulnerability management process, regular scans enable continuous, automated vulnerability scanning.
Why Vulnerability Management Is Critical
Unidentified or unpatched vulnerabilities are among the most common causes of successful cyberattacks. Without structured vulnerability management, security gaps often remain open for weeks
or even months—more than enough time for attackers.
A professional vulnerability management program delivers:
- A significantly reduced attack surface
- Clear visibility into the organization’s security posture
- Support for compliance and audit requirements
- Greater resilience across hybrid and distributed IT environments
The vulnerability management lifecycle ensures that vulnerabilities are not just discovered, but handled in a consistent, traceable, and sustainable way.
Conclusion: Vulnerability Management as an Ongoing Responsibility
Vulnerability management is not a nice-to-have—it is a fundamental requirement for modern cybersecurity. Only organizations that continuously identify, assess, and remediate vulnerabilities
can stay one step ahead of attackers.
A clearly defined vulnerability management process, supported by the right vulnerability management tools, makes vulnerability management predictable, efficient, and sustainable.