Cyber Defense
Endpoint encryption, antivirus protection and password management
Your system belongs to you and no one else. To ensure that this remains the case, Defense Control helps you prevent unauthorized access to your IT infrastructure.
Our cyber defense software supports you with efficient native Microsoft Defender Antivirus and Microsoft BitLocker Management as well as with the baramundi Local Administrator Password Solution (baramundi LAPS), wich offers an alternative to Windows LAPS that even allows you to control endpoints that are offline or outside the local network.
Your Benefits with Cyber Defense
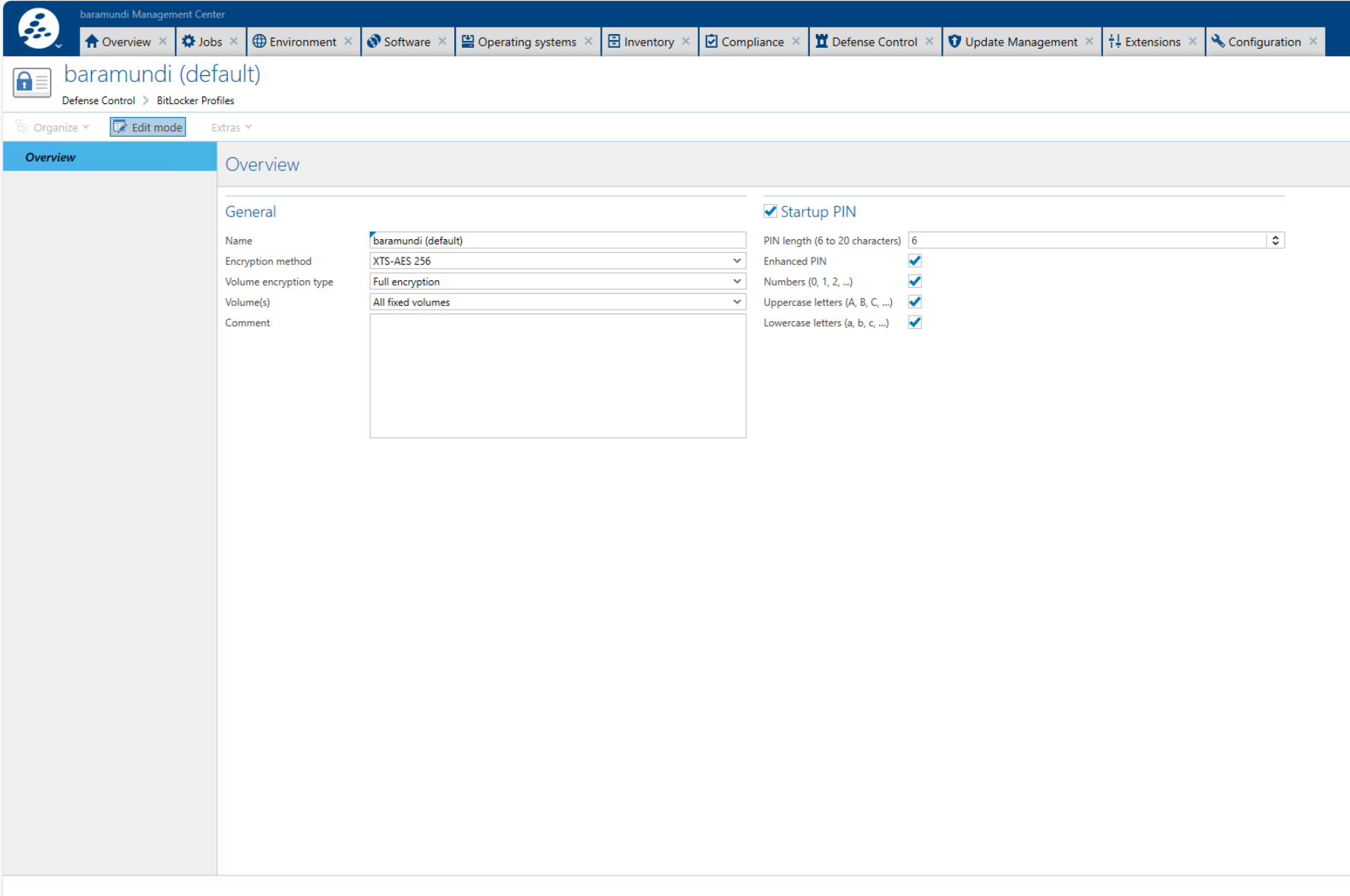
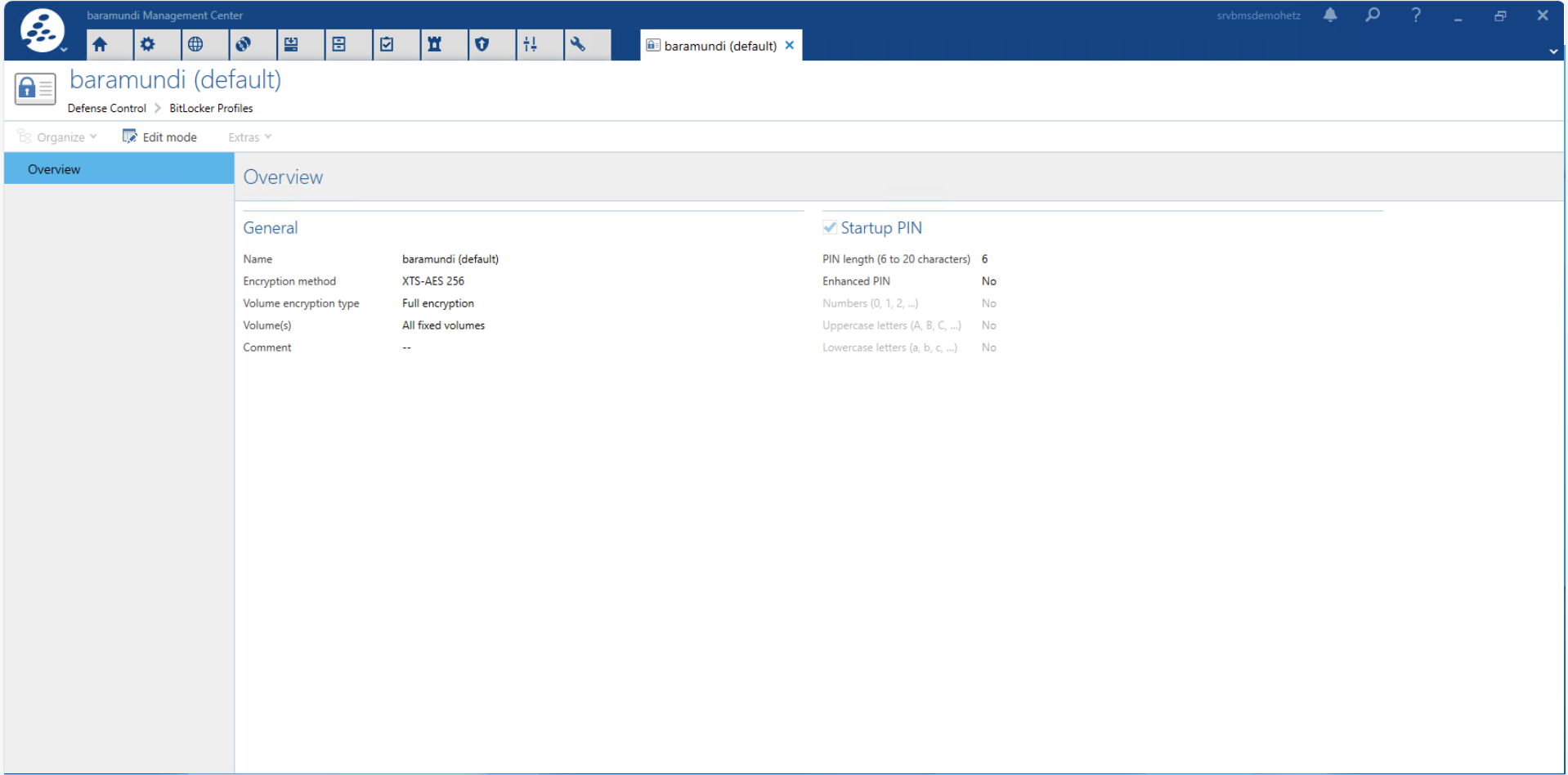
Reliable endpoint encryption through transparent Microsoft BitLocker administration
Quick configuration of Microsoft Security Tools through individual profiles
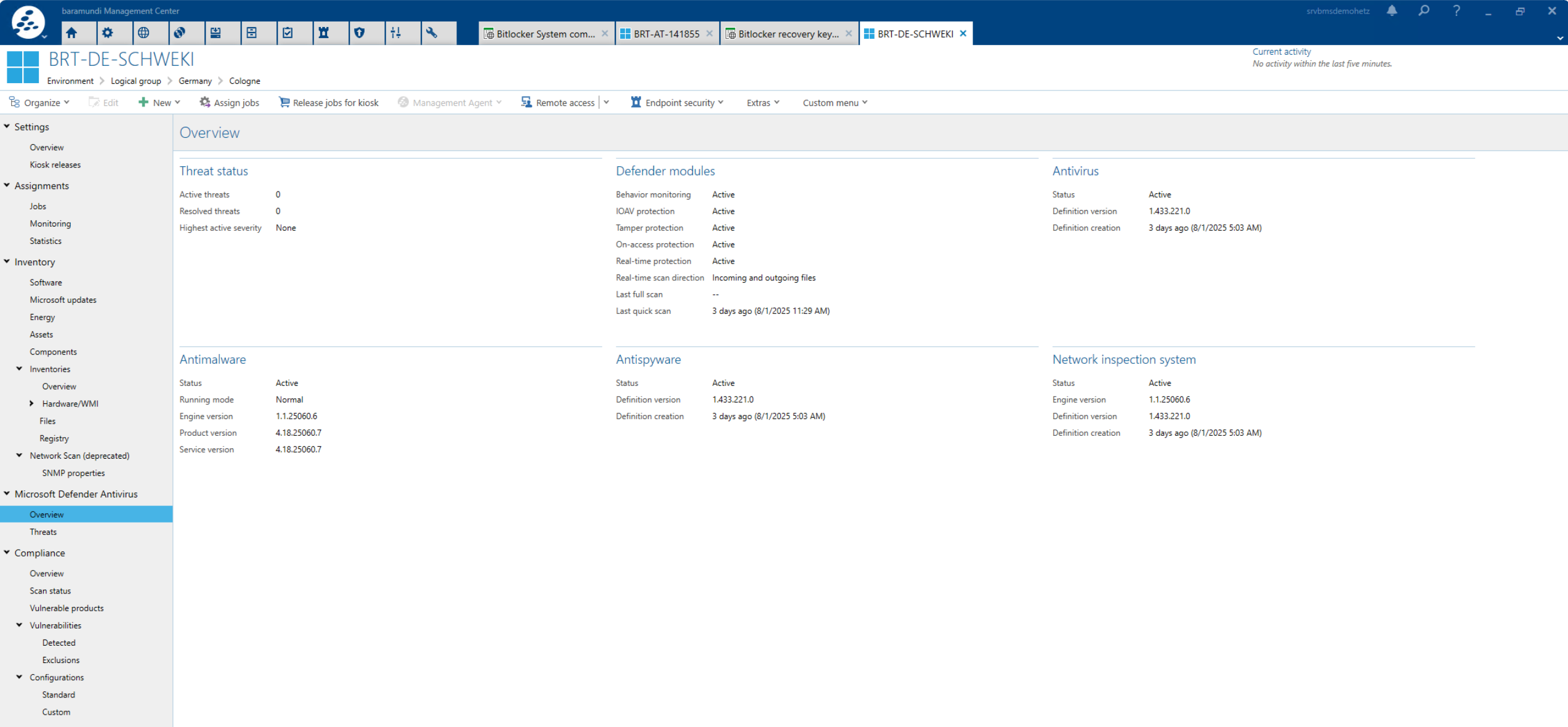
Detailed overview and comprehensive control of Microsoft Defender Antivirus management
Easy updating of local admin passwords
Key Functions for Cyber Defense with baramundi
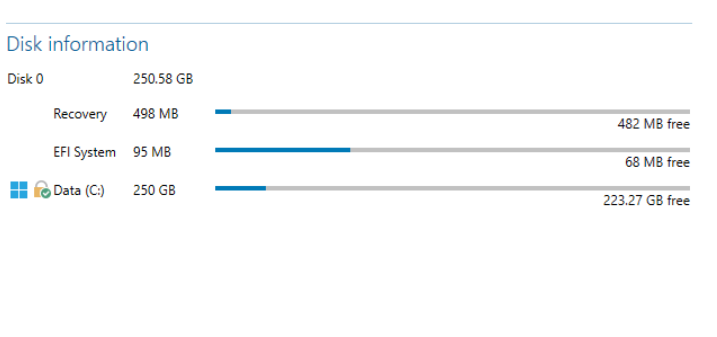
- Inventory of Trusted Platform Module (TPM) and Microsoft BitLocker management
- Control of Microsoft BitLocker administration
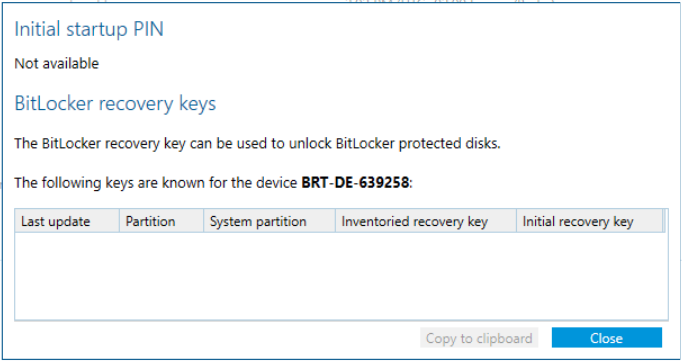
- Assignment of initial unlock passwords
- Management of recovery keys
- Granular authorization for sensitive Microsoft BitLocker administration
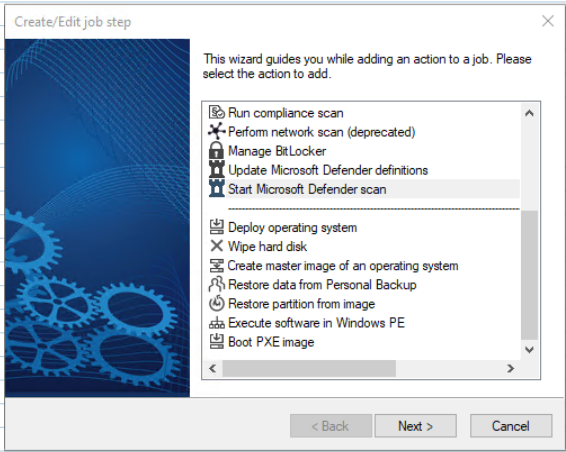
- Update of virus definitions per job
- Triggering of scans and cleanup per job
- Central management of Windows Local Admin Password Solution
Cyber Defense in Detail
Easy Management of Native Microsoft Security Tools
Resolve Virus Threats Centrally
Efficient Password Management
Do you wish to try out the baramundi Management Suite?
Request now!
FAQ: Cyber Defense
What is Cyber Defense and why is it indispensable today?
What is baramundi Local Admin Password Solution?
What is Endpoint Encrypting and how does baramundi support it?
How can I efficiently manage Microsoft BitLocker administration on my company’s endpoints?
Which Microsoft tools can I manage or replace with Cyber Defense?
Windows LAPS is fully replaced by baramundi Local Admin Password Solution:

ISO 27001: Certified Information Security
baramundi is ISO/IEC 27001 certified, the globally recognized standard for Information Security Management Systems (ISMS).
This certification confirms that baramundi meets the essential requirements for the systematic protection and secure management of sensitive information, including both customer and company data.