
IT Security Automation: Practical Vulnerability & Patch Management
There’s little if any question if IT managers should devise and maintain consistent endpoint security practices. In fact, having a formal data security plan is a legally required in many jurisdictions. However, the never-ending increase in the numbers and type of endpoints and the vulnerabilities affecting them has escalated already-heavy IT workloads.
On top of that, the sudden at-scale move to remote workforces combined with expanding digital transformation projects has some IT admins asking not just “how” to keep up with security needs, but “when” or sometimes even “if.”
There are only so many hours in a day and security tasks sometimes must be deferred in favor of regular endpoint provisioning and support as well as higher priority projects. The solution is not to learn how to become comfortable making the least-worst decision, but to change the entire dynamic by using automation. Doing that begins by answering three questions:
- Which components of modern UEM solutions are available to automate vulnerability and patch management while improving overall network transparency?
- Are those components reliable enough to provide meaningful security and ROI?
- Could the same level of security and transparency be achieved at lower cost through manual processes?
Components of automation
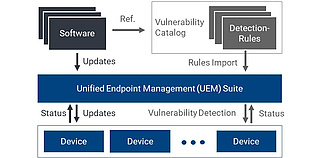
Automated vulnerability management is the successful interaction of the following components of a UEM solution.
Software updates
Regular updates from software vendors provide functional improvements as well as security fixes. The most prominent examples are Windows and other operating systems, web browsers and common
productivity apps. Obtaining, testing and deploying those updates in a comprehensive way means having a current and detailed inventory of every endpoint. That includes installed OS and app
version levels as well as available storage and installed I/O hardware on each device.
Endpoint vulnerabilities
You need to match your endpoint inventory against lists of the known vulnerabilities affecting them. Various private and governmental organizations maintain catalogs of vulnerabilities and
update them continuously with new findings reported by software vendors and trusted third parties. It’s a staggeringly large list that grows relentlessly. For example, at the end of 2020,
the National Vulnerability Database (NVD) maintained by the U.S. National Institute of Standards and Technology (NIST)
lists more than 3,000 vulnerabilities for the Windows 10 operating system alone, including 900+ new vulnerabilities added during the year. Common Vulnerabilities and Exploits (CVEs) in
widely used apps and firmware make the total number of potential vulnerabilities affecting virtually all networks far greater.
Detection rules
In order to be able to detect vulnerabilities as well as the severity of risk and urgency of applying an update requires a detailed endpoint assessment based on machine-readable rules and
scanning algorithms. At the end of 2020 there were approximately 35,000 vulnerability detection rules for different versions of Windows and associated applications. That’s a big
number, and it only applies to business IT systems. There are other vulnerability catalogs specifically for industrial equipment or Operational Technology (OT) devices deployed in
production environments.
The automation cycle
All of that complexity demands not just automation, but a structured, cyclical risk assessment and amelioration process.
Software installed on each networked device should be inventoried regularly. This can be done weekly or even daily depending on internal requirements and the risk profile for each device and its intended use. What matters most is that endpoint inventories are updated continuously and not merely as time allows. Keep in mind that an inventory must apply to both IT and OT devices and include network topology maps to identify possible points of intrusion.
At that point, IT admins plans for when new patches will be deployed. Updates and security patches are typically distributed at regular intervals, such as Microsoft's
monthly Patch Tuesday.
How reliable is automation?
The automation solution described here is based on two independent processes that together provide a very high level of overlapping safety and reliability:
1. Update and Patch Automation: Update and patch management relies on updates provided by software vendors and automatically installed on applicable endpoints. Basically, you trust the vendor and its update mechanism. There may be instances where you want to pre-test updates to avoid problems from unexpected incompatibilities, but vendor updates generally give you a solid starting point for endpoint security.
2. Vulnerability Automation: Scanning for vulnerabilities is done independently. Scanning relies on continuously updated catalogs of CVEs, your current endpoint inventory and a scanning algorithm that provides a second, vendor-independent view of device vulnerabilities.
A UEM solution not only includes both processes, it maintains detailed real-time inventories of endpoint devices and mechanisms for testing and deploying updates and patches automatically to minimize the need for user intervention or disruption. For IT managers, a well-engineered UEM solution is a comprehensive tool that delivers safety and confidence in security processes.
What about manual processes?
Can the same level of safety be achieved at lower cost through carefully conducted manual procedures? Simple math provides an answer: multiply the number of existing devices by the weekly time required for updates and vulnerability checks. The result will quickly show a rapid return on the acquisition costs of a UEM automation solution along with a higher level of performance and security. Without automation, regular inventory and vulnerability scanning is impractical. That means that security vulnerabilities will remain undetected for longer periods and create a larger number of attack vectors and surfaces.
That is why businesses and governmental agencies, especially those with smaller IT staffs and lean operations, increasingly are turning to UEM. The same applies to financial services and healthcare organizations of all sizes with robust IT security and management needs.
UEM automation effectively eliminates the “if” and answers the “how” and “when” of IT security. Even better, it makes it possible to automate routine, time-consuming IT
tasks and to free staff time for higher priority work and skills training.


